| Exhibit 10.1 | ||||||||||||||||||||
| 11111 | 11111111 | 01 I~0 0111 I~~I | II | |||||||||||||||||
| 101 1101 ~ | 1010 | |||||||||||||||||||
| US006330317B | ||||||||||||||||||||
| 1 | IIII~ | |||||||||||||||||||
| ~I | ||||||||||||||||||||
| VII | ||||||||||||||||||||
| 1111 | ||||||||||||||||||||
| (1 | Unite State Patent | (10) | Patent No.: US | 6,330,317 Bi | ||||||||||||||||
| 2) | ||||||||||||||||||||
| d | s | |||||||||||||||||||
| Garfinke | (45) | Date of Patent: | I)ec.11, | |||||||||||||||||
| l | 2001 | |||||||||||||||||||
| (54) | CALL BLOCKING SYSTEM | Rogersetal | ||||||||||||||||||
| 6/19~2 | Mellon | 379/189 | ||||||||||||||||||
| (76) | Inventor:DeanGarfinkel, 255 Piping Rock | 4,346,2 | 8/1982 | Sharvit | 379/198 | |||||||||||||||
| Rd., OldBrookville,NY (US) | 64 | |||||||||||||||||||
| 11545 | 4,358,640 | 11/1982 | Murray | 3791200 | ||||||||||||||||
| (*) | Notice: Subjecttoanydisclaimer, theleunof | 4,482,78 | 11/1984 | Sagaraetal | 379/200 | |||||||||||||||
| Ihis | ||||||||||||||||||||
| patent is extended or adjusted | 7 | |||||||||||||||||||
| 4,612,41 | 9/1986 | Smith | 379/200 | |||||||||||||||||
| under 35 | 9 | |||||||||||||||||||
| U.S.C. 154(b) by 0 days. | 4.794,64 | 12/1988 | Arbabzadah at at379/200 | |||||||||||||||||
| (21) | Appi. No.: 09/435,955 | 2 | ||||||||||||||||||
| (22) | Filed: | Nov. | 31 | |||||||||||||||||
| 9, 1999 | ||||||||||||||||||||
| (51) | hit.Cl.7 | HO4M1/663;HO4M 1/665; | ||||||||||||||||||
| HO4M11677 | ||||||||||||||||||||
| (52) | US.CI | 379/196; 379/197;379/900 | ||||||||||||||||||
| (58) | Field of Search | 379/188, 196. | ||||||||||||||||||
| 379/197, 198, 199, 200, 900 | ||||||||||||||||||||
| (56) | ReferencesCited | |||||||||||||||||||
U.S.PAIENT
34
DOCUMENTS33
| 31 |
| 3 5 |
| 3,920,93 | Mogtader | |||
| 6 | C~~d.CaI |
| ' U |
| 4,866,76 | 9/1989 | Piatar | 379/200 | |||||
| 2 | ||||||||
| 4,993,06 | 2/1991 | Dulaat al379/88.27 | ||||||
| 2 | ||||||||
| 5,161,18 | Zwick | |||||||
| 1 | ||||||||
| 5,200,99 | 4/1993 | Gaukelat at | 379/200 | |||||
| 5 | ||||||||
| 5,553,12 | 9/1996 | Grimes | 379/211 | |||||
| 8 | ||||||||
| 5,737,4 | 41199 | Zave | - | 319/201 | ||||
| 03 | 8 | |||||||
| 5,751,80 | Axlon | |||||||
| 0 | ||||||||
| Bingamcnat al | ||||||||
| 37 | ||||||||
| 9/88.12 X | ||||||||
| 6 | Fotta. | |||||||
| *cited by examiner | ||||||||
| Pnmar Examiner-HarryS. Hong | ||||||||
| (57) | ABSTRACT | |||||||
The integration ofvariousfederally requiredandstatemandated do-not-calllistsfor telemarketers into a system that automatically blocksoutgoingcalls from anumber ofcompanies ("Customer Companies") taking into accountfactors suchaspreexisting customers which may legally he contacted is disclosed.The system reviews outgoingcallsby atelemarketer, comparesit to the general do-not-call lists and thespecificcustomer company do-not-calllist andoverride permitted calllIsttomake a determination ifthecall should be. completed. This integration is due to theincorporationof a generalpurposecomputer in a central location that isconnectedto all the majortelephonecarriers switch clusterlocationsandoperated by a service provider. The "do-not-call"databaseoforiginating/destination pails,as well as the logic forblockingorpermittingtelephone calls, isstoredinthis computer.This computer makesallblockingdecisionsin real-timebasedon theoriginating anddestinationnumbercombinationsof thecall.
10 ClaIms, 6DrawIng Sheets
| U.S. | Sheet I of 6 | US | ||
| 6,330,317 | ||||
| Patent | Bi | |||
| Dec. 11,2001 |
| U.S. | US | |
| Patent | 6,330,317 | |
| Dec.11,2001 | Bi | |
| Sheet 2 of 6 |
| U.S. | 48 | 49 | ||||
| 47 | US | |||||
| Patent | Sheet 3 of 6 | 6,330,317 | ||||
| 74 | B! | |||||
| 48 | 77 | |||||
| Dec. 11,2001 |
| 61 |
| Dec.11,2001 |
| 55 |
| .56 |
| Is there.CN |
| 5 7 |
5859
| ~Yes~~fl |
| 60 |
| 66 65 |
| Yes |
78
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||
| 85 | ||||||||
| U.S. Patent | Dec. 11,2001 | Sheet5of | 80 | |||||
| US 6,330,317 Bi | ||||||||
| [Customer Logson to Internet |
| ~ 8 |
| 4 |
| 8 andPasswo |

FIG. 4
| 92 | ||||||||||
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||||
| U.S. Patent | Dec. 11, | |||||||||
| 2001 | ||||||||||
| Sheet 6 of 6 | ||||||||||
| US | ||||||||||
| 6,330,317 | ||||||||||
| B! | 9 | |||||||||
| 1 | ||||||||||
| Disable Internet | ||
| Site | ||
| 1~ | ||
| Bulk Copy | ||
| Updating | ||
| Database | ||
| .4. | ||
| Re~Enable Internet | ||
| Site | 93 | |
| :____ | ||
| formatfiles | ||
| ! | ||
| ReplaceControl | ||
| Computer | ||
| Database with | ||
| Reformated | ||
| Updating | ||
| Database | ||
FIG. 4
| U.S. Patent |
| Sheet 4 of 6 |
| US 6,330,317 Bi |
| FIG. 7 |
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||
| US 6,330,317 BI | ||||||
| 1 | 65 not eliminate the possibility of an employee innocently | |||||
| CALL BLOCKINGSYSTEM | calling a numberfrom an oldcalllist or an employee | |||||
| simply | ||||||
| BACKGROUND OF THE | 2 | |||||
| INVENTION | disregarding the company's do-not-calllistaltogether in | |||||
| 1. Field of the Invention | thesearchfor commissions. | |||||
| ilie inventionconcernstelephone systems generally and | In addition,certainambiguities develop in use. For | |||||
| more specifically,concernsthe blocking of outgoingphone | example, a prior purchaser may have placed hisnameon a | |||||
callsto phone numbers which have been placed on ado-state mandatedlist. Thehandprocesswouldeliminatethat
| not-call list. | number although the customer may, in fact,wishto | |||
| 2.PriorAir | receive the call and byhisformer purchases, is apermitted |
Inrecent yearsthe door to doorsalesmanhas been callee replaced by telephonesolicitation.Rather than a salesmanunderthestatelaw.
walkinga route, a telemarketermakes a seriesof telephoneVariousattempts have been made to control out-calls. The telephonenumbers dialed are normallyon a call going ~ calls, usually to restrict longdistancetoll calls or to list given to thetelernarketing salesmanby his employer. The a single calllistmay beorganizedby address,consumerinformationListofrestricted numbers.A number of systems have or bythe numbers themselves. Just astheconsumerbeen can slamthedoor in thefaceof a door to doorsalesman,thedirectedto stopping themakingof longdistance callsorconsumermayhangupupon receivinga telephone solici-specific area callsfrom a givenlocation.For example, US. tation. However, thecallitself isconsideredbymanytobe Pat.No. 4,612,419, toSmith,entitled Toll Restriction anintrusiveact. The widespread nature of telephone solici-Cii15cultforElectronicTelephone Station,describesa tationmeansthatcertainsegments ofthepublicare desirousmeans ofbeing protected fromeven receIving suchcalls. Thus, a controllingtollcallsonlyandis employed within the number ofprivate organizations werecreated toinform directtelephone stationitself.Itlooksfor a 0and1 in the firstmarketers astothosewhodidnot wish to receive such dialeddigit,the subscriber can lock andunlockthe device phone calls. Organizations produced do-not-call lists from by a key those who do not wish to receive tolemarketingsolicitationspad entry with an enabling anddisablingcode. U.S.andprovided suchliststo thosedirect marketeerswho Pat. No.
| voluntarilycomply with theconsumer'srequest.Upon | '° | 4,358,640, to Murray, entitled TelephoneSecurity | ||
| receipt ofthese lists, thesemarketeers would delete thelisted | Device, issued Nov. 9, 1982,describesa circuit whichhas | |||
| numbers fromtheir telemarketer'scalllists. Such do not call | means to | |||
| listsworkboth to thebenefit of thepeople whodonot wishto | allow or disallow toll calls onentryof aprogrammable code | |||
| receive callsandto the soliciting company whichhas its call | stored. U.S. Pat. No. 4,794,642, to Arbabzadah Ct at., | |||
| list referredto a moreselectgroup of potential consumers | Call | |||
| thatare morereceptive of telephone sales pitches. | - | Screeningin a Public Telephone Station, issued Dcc. 27, | ||
| The FederalGovernment requireseach telemarketer to | 2) | 1988,disclosescontrolequipment in acustomer owned | ||
| maintainits own 'do-not-call" lists andto add to the list the | public telephone station which prevents auser from | |||
nameof anyone sorequestingexclusion from telephonecalls making unauthorizedtelephonecallsin a telephone system.from their company.Under the statute, fines can be assessed The
against companies that call numbers onthe company'sdo-system restrictstelephonenumbers a user candial to those not-calllist.The consumer is given the right to sueany numberspreselected by a station owner. U.S. Pat. No.30company whichcallsthem aftertheyhaverequestedthat the 5,200,995, to Gaukel et at.,issuedApr. 6, 1993, entitled company place them on thedo-not-calllist. Inaddition, aUniversalOutgoing CallRestrictionCircuit, discloses a numberofstategovernments, includingthose of florida,circuit which prevents a telephone or a plurality of tele-Oregon,Arizona, Alaska,Kentucky, Tennessee,Alabama,phones frommaking unauthorizedorrestricted calls to Arkansas and Georgia, maintain,or in thenear future,will be specificnumbersorunspecificgroups of numbers.Essen maintaining,statewide do-not-call lists which arc applicable~ tiallythe systemcomparesthenumbers againstprepro-to all vendorscalling numbersinthestate. grammed internal lists of restricted numbers.Thus, atelemarketer is faced with a legalresponsibilityNone of these patentsdisclose a system necessaryto
under federal and stalelaw torefrainfrom callingnumbers handle theblockingrequirementsunder federalandstatemaintainedonseparate listsincludingtheir own internal listlaw and listspreparedbyvariousblocking organizations. andlistsmaintained by anumberof stategovernments.On
| penalty offine andcivil action, theresponsibility islaidon | SUMMARY OF THEINVENTION | |||||
| the telemarketer toensurethat no do-not-callnumbers are, | Asystem which would monitor andquicklyupdate all | |||||
| in fact, called. Inaddition,they may have one or more | such lists for a numberof companieswould be beneficial | |||||
| organizations do-not-call list with which the telemarketer | to | |||||
| wishes to comply. Accordingly, companies developedtheir | ~ | boththeconsumerswho wish to be protected from | ||||
| final call lists fortheirtelemarkcter bycomparingand | telephone | |||||
| matching their federaUyre~uire.ddo-not-call list,various | solicitationand the soliciting companies. Such asystem | |||||
| state | do-not-call listsandorganizational do-not-calllist-s | would have to be able to block or specifically permit calls | ||||
| with | their telemarketer's call listsandeliminatinganyfrom specificoriginatingnumbers tospecific destination | |||||
| matchingnumbers fromtheir calllist. Thisprocess has until | numbers. To beuseful,the do-not-call decision would | |||||
| now been done manually and is subject to human error. | have so to befullyautomatic and include the capability | |||||
| There is a large number of employees who must be com- | of dynamically changingthedo-not-call list for specific | |||||
| mitted to this effort. Even with thiseffort,theprocess does | originating/ | |||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||
| destinationphone numberpairsas individuals request | 60 supporting a single company specific do-not-call list for | |||||
| blocking or becomeclientsof the company in question. | multiple offices ofthe samecompany in different | |||||
| Each | geographiclocations. Finally,it must be able to import, in | |||||
| callingcompanymustbe capable of adding ordeleting ~ | bulk, large numbers of specific telephone number | |||||
| numbersfromthecompany'sspecificdo-not-call list | combinations. | |||||
| without affecting another company'slist. Equally,each | The present invention isdirectedto integration of | |||||
| company | various do-not-call lists into a systemthatautomatically | |||||
| must have theoptionof automatically blockingnumberson | blocksoutgoing calls from a number of companies | |||||
| the state mandated list or to block only from theirown | ("Customer Companies") taking into account factors such | |||||
| do-not-call list.Equally such a systemmustbe capable of | as preexisting | |||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||||||||||||||||||||||||||
| US 6,330,317 Bi | ||||||||||||||||||||||||||||||||
| 3 | FUll.7is a flow diagram for transferringthe updated | |||||||||||||||||||||||||||||||
| customerswhich may legally becontacted. Thus,rathcrthan | database informationto the controlcomputers, | |||||||||||||||||||||||||||||||
| modifying the call lists for each customer company,it actsto | ||||||||||||||||||||||||||||||||
| review the outgoing call, compare it to the. general do-not-call | DETAILED DESCRIPTIONOF NE | |||||||||||||||||||||||||||||||
| lists andthespecific customer companydo-not-call listand | PREFERREDEMBODIMENTS | |||||||||||||||||||||||||||||||
| override permitted call listtomake a determi- ~ nationif the | ||||||||||||||||||||||||||||||||
| call should becompleted. This integration is due to the | The presentinvention encompasses not onlythe specific | |||||||||||||||||||||||||||||||
| incorporationof a generalpurpose computer in a central | methodof blockingthetelephonecalls butofmaintaining | |||||||||||||||||||||||||||||||
| locationthatis connected toall the major telephonecarriers | and updating the do-not-call database andits component | |||||||||||||||||||||||||||||||
| switch duster locations and operatedbya serviceprovider. | lists | both | in | general and | for specific | customer | ||||||||||||||||||||||||||
| The "do-not-call" database of originating/destination pairs, | companies. In | |||||||||||||||||||||||||||||||
| as well as the logic forblockingorpermitting telephonecalls, | ~ particular | the | invention | includes | the | periodic | ||||||||||||||||||||||||||
| is stored in this central computer. This computer makes all | synchronizing | |||||||||||||||||||||||||||||||
| blocking decisionsinreal-time basedon theoriginating and | of the do-not-call | databaseswith amaster | updating | |||||||||||||||||||||||||||||
| destinationnumbercombinationsofthe call. | database which is periodically updated by customers through | |||||||||||||||||||||||||||||||
| All participating customer companies have access to a | the internetand bystate and consumer organizations latest | |||||||||||||||||||||||||||||||
| separate part of this database ("updating do-not-calldatabase") | do-not-call lists. | |||||||||||||||||||||||||||||||
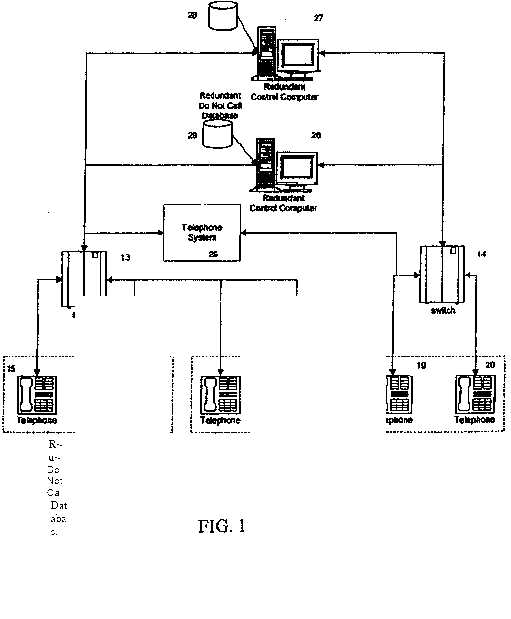
| for the purposeofaddingordeleting numbersontheir | FIG. | 1 is | adiagrammatic representation | of | how the | |||||||||||||||||||||||||||
| company specific do-not-call lists or to permit override of | control | computer | of the | presentinvention | interconnects | |||||||||||||||||||||||||||
| specific numbers on any state mandated or organizational do- | withthe normaltelephone system. Telemarketingcustomer | |||||||||||||||||||||||||||||||
| not-call lists. Since this database receives information from | companies10-12 receive their telephone services fromone | |||||||||||||||||||||||||||||||
| various companies and from a number of state and | ormore telephone | companiesor carriers. The | customer | |||||||||||||||||||||||||||||
| organizational do-not-call lists, it must be accessiblefrom | companies | 10-12 | arc | connected | to | its | own | |||||||||||||||||||||||||
| different geographical locations. Accordingly, the database is | telecommunications company | provider by | conventional | |||||||||||||||||||||||||||||
| maintained using the Internet.TheInternet acts as a customer | means suchas plain old telephoneservice lines (POTS), Ti | |||||||||||||||||||||||||||||||
| interface that willpermitany customerwho hasaccessto the | line, feature | I),orany | other | conventional | telephonic | |||||||||||||||||||||||||||
| Internet to enter change requests forspecific do-not-call | linkage. The | telecotnrmmication company provides a dial | ||||||||||||||||||||||||||||||
| lists. | tone to thecustomerfor atclepbone call and performs all | |||||||||||||||||||||||||||||||
| Undernorrnal telephone practicewhen a call isoriginated, | normal communication functions. Calls are placed from hand | |||||||||||||||||||||||||||||||
| theinformationfor the call istransported totheprimary ~ | sets15-20 at | therespective customers10-12 to | their | local | ||||||||||||||||||||||||||||
| switch clusterfor thetelecommunications carrier. This infor- | primarytelephone switchcluster13-14. | |||||||||||||||||||||||||||||||
| mation includes both the originating number, or where the | As seen in FIG. 1, customer companies10and11 havetheir | |||||||||||||||||||||||||||||||
| caller has a trunk line, the AuthCode (a seven digit number | telephone | service provided through thesame primary | ||||||||||||||||||||||||||||||
| corresponding to the originating trunk group of the caller) and | switch cluster | 13. | Customercompany | 12, | has its | |||||||||||||||||||||||||||
| the called number('originatirig/destination pair"). If the caller is | telephone | service | provided | through | primary | switch | ||||||||||||||||||||||||||
| from a participating customer companyonthe present do-not- | cluster14. As isnormal with any telephone call, when a | |||||||||||||||||||||||||||||||
| call blocking system, the switch cluster recognizes the | call is placed from handsets15-19 information both as | |||||||||||||||||||||||||||||||
| originating number or authorization code and the | to theoriginatingnumber ofthe hand setand the | |||||||||||||||||||||||||||||||
| originating/destination pair information is transported from the | destinationnumber whichwasdialed by the customer | |||||||||||||||||||||||||||||||
| switch cluster to the control computer while the call is held at | company | (i.e., | the | originaling/ | destination pair) is | |||||||||||||||||||||||||||
| ,~ | ||||||||||||||||||||||||||||||||
| the switch cluster. The control computer's function is to then | supplied | to theswitch | cluster | 13-14. | In | normal | ||||||||||||||||||||||||||
| process the information and create a command to either block | operation, the primary switch cluster 13 and 14 would | |||||||||||||||||||||||||||||||
| that call or permit the callto becompleted. Once the decision is | then route thesignaltothedestination number dialed | |||||||||||||||||||||||||||||||
| made, the control computer indicates the. decision to the | at the respective | telemarketer's | hand | sets | 13-20 | |||||||||||||||||||||||||||
| carrier's switch cluster and a command is implementedatthe | throughthetelephone system 25. In thepresentsystem, | |||||||||||||||||||||||||||||||
| switch cluster to either allow the call to be completed or to | the | switch | cluster | 13-14 | determinesfrom | the | ||||||||||||||||||||||||||
| return a message tothetelernarkctcr indicating that it has been | originating | numberor | AuthCode whetherthe call | is to | ||||||||||||||||||||||||||||
| blocked under the call blocking system. | be reviewedfora do not call determination. If the | |||||||||||||||||||||||||||||||
| originating number is one of the numbers fromwhich | ||||||||||||||||||||||||||||||||
| BRIEF DESCRIPTION OF ThE DRAWINGS | calls are to be reviewed, theswitchcluster 13-14 | |||||||||||||||||||||||||||||||
| The invention canbe more fully understood fromcon- | holds thecalland forwards theoriginatingdestination | |||||||||||||||||||||||||||||||
| siderationof the following detaileddescriptionof anillus- | pair to acontrolcomputer 26-27 for a determination | |||||||||||||||||||||||||||||||
| trative embodimentofthe invention andthe accompanying | of whether the callshouki be madeor blocked by | |||||||||||||||||||||||||||||||
| drawings inwhich: | so reference totheirrespective databases either stored on | |||||||||||||||||||||||||||||||
| FIG.1 is adiagrammaticrepresentation of thecomponents | that computer | 26-27 or inseparate | storage means | |||||||||||||||||||||||||||||
| ofthecontrol system; | 28-29. | |||||||||||||||||||||||||||||||
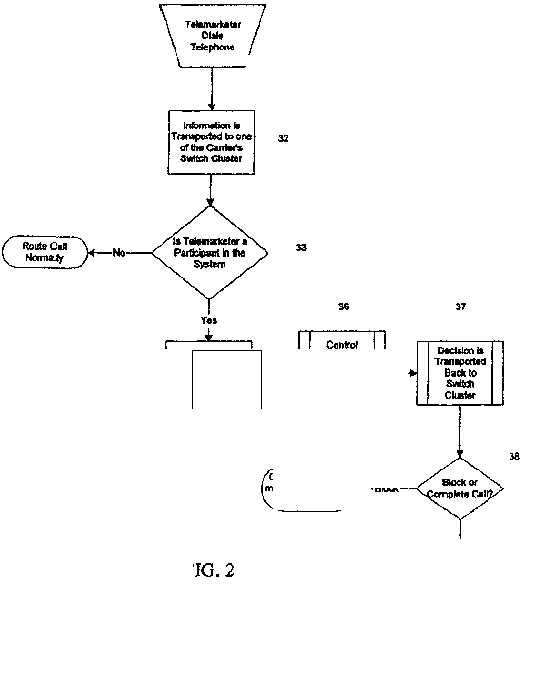
| FIG.2is a flow diagram showing the overallcallblock | Inactuality,there | may | be | two | or | more | redundant | |||||||||||||||||||||||||
| processing; | controlcomputers26-27 performing the function. While | |||||||||||||||||||||||||||||||
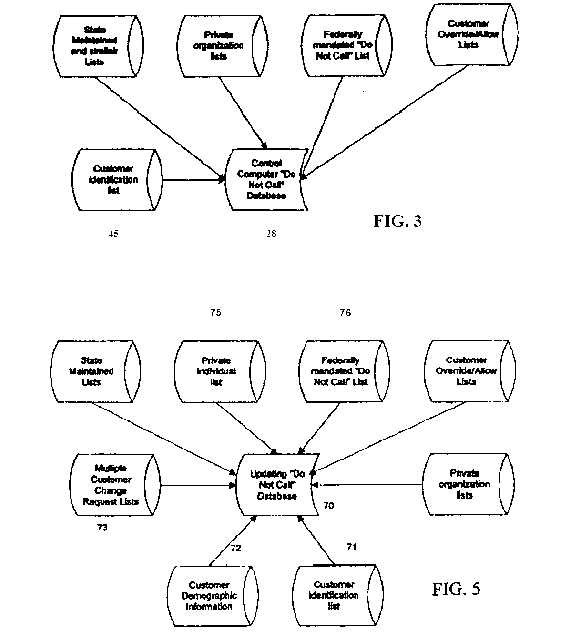
| FIG.3 is a diagrammaticrepresentationof thevarious | eachsuch | |||||||||||||||||||||||||||||||
| elements forming the control computer do-not-call database; | computer will bedesignedtohandlethecompleteload | |||||||||||||||||||||||||||||||
| FIG.4is a flow diagram of decision making process | of s~c anticipated call traffic, the traffic loadmaybe | |||||||||||||||||||||||||||||||
| performed by the control computer; | divided evenly | |||||||||||||||||||||||||||||||
| FIG.5is a diagrammatic representation of the components | betweentheredundantcomputers26-27. Thus, ifone | |||||||||||||||||||||||||||||||
| of thesystemto update the do-not-call database; | of the control computers 26 cannothandlea callmutedto | |||||||||||||||||||||||||||||||
| FIG. 6 is a flowdiagram ofdata entryto thecustomer's | it for any reason, one of the alternative control computers | |||||||||||||||||||||||||||||||
| do-not-call database by the Internet; | 27 can | |||||||||||||||||||||||||||||||
| automatically take over.Although shownas two | ||||||||||||||||||||||||||||||||
| 4 | computers 60 inFIG.1, a number of such redundant | |||||||||||||||||||||||||||||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||
| computersmay be | 65 more easily adapted to handle. numerous wide-spread | |||||
| used and, infact,such | controlcomputersmay beoffices | |||||
| geographicallydistributedthroughout thecountry, creatinga | of asingle companyin a uniform manner. Ofcourse, | |||||
| system with multiplexredundanciesand, therefore, | the do not call database 28-29 for each of the redundant | |||||
| extremely high | computers | |||||
| reliability. Geographicdistribution also makesthis system | ||||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||||||||||||
| US 6,330,317 Bi | ||||||||||||||||||
| 5 | nwnber. | |||||||||||||||||
| wouldhaveduplicate information and their updating be | Since the state mandated lists are for all telcmarketing | |||||||||||||||||
| improved so thateach blocking computer 26-27 would | done within the state regardless of the source, theyarenot | |||||||||||||||||
| respondin the same way inmaking acallblockingdecision. | taggedfor, orassociated with,individual customers. Similar | |||||||||||||||||
| FIG.2 is a flow diagramshowingtheprocessfor | do-not-calllists are maintainedby private organizationsare | |||||||||||||||||
| blocking | not customer companyspecific4'7.Such lists areforall | |||||||||||||||||
| anindividualtelephone call. The telemarketer of a | relemarketcrsand arethus nottaggedby customer compa- | |||||||||||||||||
| customer | nies. List 48 isthefederally required do-not-calllistwhich | |||||||||||||||||
| company10-12dialshis handset15-20 in aconventional | mustbe maintained by each telemarketer. Thislistis a 65 | |||||||||||||||||
| manner 31. Asnormalin modem telecommunications, | compilationof allthoseindividuals who, when called by a | |||||||||||||||||
| by so dialing thehandset 15-20,the customer | customercompany 10-U,indicatedthatthey wishedno | |||||||||||||||||
| company 10-13 | 6 | |||||||||||||||||
| originatesa signalcorrespondingboth to | thedialer's | furthercalls. Sinceeachsuch list is peculiarto thecustomer | ||||||||||||||||
| originating telephonenumberor where the handset is | company,it is tagged with the customer company's CM. | |||||||||||||||||
| on aprivatetrunk line,itsAuthCode, and the | The | |||||||||||||||||
| destination number,i.e.,theoriginating/destination pair. | finallist49formingeachredundant database 28-29 isthe | |||||||||||||||||
| This information istransportedin thenormalmanner | customer company's override/allow lists. The | |||||||||||||||||
| 32 to the telcmarketcr's telecornmunication | ||||||||||||||||||
| company's carrier's primaryswitch cluster13-14. | customer | |||||||||||||||||
| Atthecluster, the switch 13-14 determines if the | ~company may haveestablished relationswith one or | |||||||||||||||||
| calloriginates[mm a handset 15-20 which is subject | more | |||||||||||||||||
| to call | individuals who, while unwillingtoaccept telemarketing | |||||||||||||||||
| blocking 33.Ifnot,the callis then automaticallymuted | callsin general. arewillingto accepttelemarketing calls | |||||||||||||||||
| normally 34 to the | destination telephone number. | fromthis particular customer company.Thislist contains | ||||||||||||||||
| However, when thecall originatesfrom a telephone | all | |||||||||||||||||
| handset15-16 | such numbersfor a customer companyand is tagged with | |||||||||||||||||
| which is subjecttoblockin& the call is so recognizedby the | the 10customer company's CM to permit callstosuch persons | |||||||||||||||||
| primary switchcluster 13-14, the call is held at the | 53 | |||||||||||||||||
| switch | by the allowed customercompany. | |||||||||||||||||
| cluster13-14 | and | theoriginating/destination | pair | FIG. 4 is a flowdiagram showing the processforcarrying | ||||||||||||||
| information istransported35 to one of thecontrol | out the Block/CompleteAlgorithm. Wben an originating/ | |||||||||||||||||
| computers 26-27.The control computer 26-27 then | destinationpair arriveat the control computer for review, it | |||||||||||||||||
| determines whether | thecallsshould bepermittedor | isfirstcompared55with the customer list45 toconfirmthat | ||||||||||||||||
| blocked by execution of ablock/complete algorithm 36as | theoriginating nurnber isthat of a customercompany. If it | |||||||||||||||||
| morefully discussed below. | Uponmaking | the | isnot, the call is completed 56. If, however, it is on the | |||||||||||||||
| appropriatedetermination,the | control computer | 26-27 | customeridentification list45,the CM for theoriginating | |||||||||||||||
| transports the decision37 to theswitch cluster13-14. | number is determined and used in obtainingthe | |||||||||||||||||
| Dependingupon thisdetermination38, either the call is | appropriate | |||||||||||||||||
| blocked 39anda message isforwardedto thetelemarketer | ~ information from lists 48 and49. | |||||||||||||||||
| 40 indicating that the callhas beenblocked or is muted | Thecalled number is thencompared 58 to thefederally | |||||||||||||||||
| normally 40. Theentire decision making process isvery | required do-not-call list 48. As previously noted, thisdo-not- | |||||||||||||||||
| rapid. It is unlikelythata lelemarketcrwill | noticeany | call list is tagged with the customercompany's CN. If the | ||||||||||||||||
| delayin placing the call. | called number is on thefederally required do-not-call list | |||||||||||||||||
| The block/completealgorithm usedto make theblock | for | |||||||||||||||||
| decision36 is based on the information in theredundant�� | ~ that customer company,thecall isblocked59. if, on the | |||||||||||||||||
| do not call databases 28-29.As seen most clearly in FIG. | other hand, the callednumberis not on the federally | |||||||||||||||||
| 3 eachredundantdatabase 28-29consistsof a number of | required | |||||||||||||||||
| component lists 45-49. The database 28-29 isstructured | list 48for thecustomercompany,i.e., the number is either | |||||||||||||||||
| around the customer | identification | list45. | This | listis | not on the list or it isnotcalledwiththe CM of thecalling | |||||||||||||
| composedof an | identification codeor | number | ("CN") for | customer company. If the same numberis to be blocked | ||||||||||||||
| each customer | and | thetelephone numbers | andIorS for :to twodifferent customer companies,thenumber appears | |||||||||||||||
| AuthCodes correspondingto each customer.Alloriginatingritwice | ||||||||||||||||||
| telephone numbers andAuthCodcsaretaggedwith the | on the do-not-call list 48, eachtime with a different tag. | |||||||||||||||||
| customer's CN.AII offices of a single companyhavea | The | |||||||||||||||||
| single CN.List45entriesmay alsocontain oneor more | number is then compared 60 to the allowed/override list49 | |||||||||||||||||
| flagscalledprivate | organization | or P0 | flags | that | 5for theparticular customer company as indicatedbythe CM | |||||||||||||
| determineswhether or | not a customerhaschosen to be | 5 | tag in theallow/override list 49. If the number is on the | |||||||||||||||
| blockedfrom calling the numbers | ononeor moreprivate | ~s allow/override list 49, the call is completed 64. If it is not | ||||||||||||||||
| organizationmaintainedlists.If the value of a P0 flagis | on | |||||||||||||||||
| false,the customer has chosennotto beblockedby that | theallow/override list49, the call number isthen | |||||||||||||||||
| private organization's | do-not-call | list. List 45allowsthe | compared61 tothe state mandated list46. Ifthecallnumber | |||||||||||||||
| control computer to selectthe relevant informationfrom | ison thestate mandated list46, the call is thenblocked62. If | |||||||||||||||||
| lists48-49 anddetermine whether to use list 47. | it isnot | |||||||||||||||||
| List 46 is a composite list of all the state generatedLists | on the statemandatedlist 46, the programsdetermines | |||||||||||||||||
| fromallrelevantstates. Tothislist may beadded | ~ whether the privateorganization dipflag is at true or | |||||||||||||||||
| individuals whohaverequestedthe service provider to be so | false | |||||||||||||||||
| protected. Theresultinglist may besortedby areacodeand | 63. 1111 is false, and thusthe customer does notwith to | |||||||||||||||||
| FIG. 4 | ||||||||||||||||||
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||
| adhere to theprivate organization's requested blocking, the | organiz.ationlists47 are periodically updated, asare | |||||
| callis completed 64. if, on the other hand, the private | allow/override lists. New customer companiesarc added to | |||||
| organizationdip flag is true and,thus, the customerwishes | the system. All these changes require that the customer | |||||
| toconformto the request oftheprivateorganization,the | identificationlist45, | |||||
| call number is thencompared65 to the private | the federallyrequireddo-not-call list 48 and thecustomer | |||||
| organization list 47. If it is not ontheprivateorganization | on override/allowlist49 beupdatedaccordingly. In order to | |||||
| list 47,thecall is completed 64. If, on the otherband,it is | keep the redundant do-not-call databases 28and29 | |||||
| on the privateorganization list47, the call is blocked. | current,thedatabasesareupdated daily with information | |||||
| Obviously, thecontentsof thedo-not-call database26-29 | received fromthecustomers and as received with regard to | |||||
| mustbe updated as the underlying information changes. | informationsuch as state mandatedlistsof do-not-call | |||||
| Atpresent,except for Alaska,thestatesissuenew state | numbers. | |||||
| mandated databases quarterly. Thefederallyrequired do- | In order to accomplisb this result, a separate updating | |||||
| no-calllist48 changes daily as people indicate they do not | do-not-calldatabase 70 is maintained on an updating com- | |||||
| desirea customer company to call them again. The private | puter(notshown) maintained by the service provider. As | |||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||||||||||
| US 6,330,317 Bi | ||||||||||||||||
| 7 | the appropriate table in the controlcomputer,thechange | |||||||||||||||
| seenin FIG. 5,the updating do-not-call database70 is | request record in the user-interface | |||||||||||||||
| composedof anumberoflistswhich areperiodically updated | S | |||||||||||||||
| as new information becomes available.One ofthe component | computer is updated withthedate ofthis addition. When | |||||||||||||||
| listsis the customeridentification list71correspondingto | the | |||||||||||||||
| the customer identificationlist45containedon the control | customer requests a deletion,a record is added tothechange | |||||||||||||||
| computerdo-not-call database 28.In normal | request table; however, in thiscase, a record isdeletedfrom | |||||||||||||||
| operation, new customer companies arc addedand customer | therequestedtable. The date of the deletion request is | |||||||||||||||
| companiesleave theservice. Equally, existing customer | part | |||||||||||||||
| companies may change ielepbonc service, addingor sub- | s of the data entered in the change request table but not in | |||||||||||||||
| trading telephone numbersorAuthCodes for the service. As | the requested table.After verification thattbe requested | |||||||||||||||
| such changes occur, they are inputted into the customer | deletion | |||||||||||||||
| identification list71 by theservice provider to produce an | has been made to theappropriatetable inthecontrol | |||||||||||||||
| updated list of telephone numbers and AulhCodes tagged | computer, the changerequestrecord in the user-interface | |||||||||||||||
| with the appropriate CN. The updatingdo-not-call database | computeris updated with the date of thisdeletion. This | |||||||||||||||
| mayalso contain customer demographicinformation 72, | ~o enablesthe customer to determine,at any time, which | |||||||||||||||
| such asfull corporate names, addresses, telephone numbers, | changeshavebeen requested in which customer lists.The | |||||||||||||||
| billing informationand thelike associated witheach CN for | customer can also determine which | changeshavebeen | ||||||||||||||
| use of theservice provider. | verified as beingwritten inthe control computer bylooking | |||||||||||||||
| As each state mandated list is received bythe service | at the date of thechange. Ifthe changehas not occurred | |||||||||||||||
| provider,the serviceprovider updates list74 toinclude any | inisthecontrol computer,the dateappears as blank; | |||||||||||||||
| newnumbers and make any otherappropriatechangesin the | otherwise, | |||||||||||||||
| list 74.State mandated listsmay be provided over the | the date of the verification | of the | change | appears. | ||||||||||||
| Internetor byCD-ROM disk, each state having itsown | Records in thechangerequest tables arc never deletedin | |||||||||||||||
| uniqueprotocols and softwareprograms. Using such | order tomaintainan audit trail of requestedcbanges. | |||||||||||||||
| programs, thedata may beconvertedto a common format | As noted above,the lists 71through78formingthe | |||||||||||||||
| forupdatingthestatemandated lists 74. | 20updating do-not-call database are updatedin a number of | |||||||||||||||
| Asnoted above, in the control computer do-not-call | differentfashions dependingon thenatureof theinforma- | |||||||||||||||
| database 28,state mandated information is combined with | tion. Customer identification lists71arc inputted directly | |||||||||||||||
| the telephonenumbersofindividuals whohave contacted | inthe updating computer by theservice provideras would | |||||||||||||||
| theservice provider and requested their name be placedon | customer demographic information 72. Equally,state | |||||||||||||||
| thelist. This information iskept on aseparate private | man- | |||||||||||||||
| individual list73 which is combined with thestate | 25dated Lists are normally suppliedby the. state on CD- | |||||||||||||||
| mandated | ROM | |||||||||||||||
| list74 tomake up a single list inthecontrol do-not-call | in anumberof differentprotocolscacb having their own | |||||||||||||||
| database 28 duringthe transferprocessof updating the | associated software. Thus,in order to make alist74 the | |||||||||||||||
| control do-not-call base28. | 35 | serviceprovider would normally have to useeach of the | ||||||||||||||
| Similarly, throughoutthebusinessday, each customer | separate typesofsoftwaretotransfer theinformation to a | |||||||||||||||
| company receives do-not-call requests from individuals.The | 30common format wheresuch information | would | be | |||||||||||||
| customer company storesthechangesandperiodically | lutegrated. | Similarly, private individuals requesting | the | |||||||||||||
| modifies federallyrequireddo-not-calllist76 maintained in | service | |||||||||||||||
| theupdating database 70. List76 is, inreality, a more current | provider place | themon a do-not-call list | would be inputted | |||||||||||||
| list of the federallyrequired do-no-call list 48 forming partof | into its separate list75 by theserviceprovider which is then | |||||||||||||||
| do-not-calldatabase 28.In alikemanner, customer | integrated in the control computer'sdatabase 28]. | |||||||||||||||
| override/allow lists may change during the day as | However, the federallyrequired do-not-call list76and | |||||||||||||||
| individuals,for example, request acall fromthecustomer | customer override/allow lists77are aproduct of the indi- | |||||||||||||||
| company and, thus, updatingdo-not-calldatabase70 main- | vidual customer'sbusinessandareperiodically changed | |||||||||||||||
| ~stains anupdatingcustomer override/allow list77. This is a | duringthe day. Ithasbeen found that thebestway for | |||||||||||||||
| more currentversion of the informationstoredin the cus- | customer companiesto forward | informationto | the | |||||||||||||
| tomeroverride/allow list49 ofthecontrol computer do-not- | updating4°do-not-call database | 70 is bymeansof | the | |||||||||||||
| call database 28. Finally,the privateorganizations periodi- | Internet. | |||||||||||||||
| cally update their list and such updated lists are maintainedon | FIG.7 is a flow diagram of the method used to upload | |||||||||||||||
| private organization list 78 of the updating do-not-call | informationfromindividualcustomers | foralteration of | ||||||||||||||
| database. This list78 is thecurrent list corresponding to | the federally | requireddo-not-call list 76 | andthe | customer | ||||||||||||
| privateorganization list47 on the control computer do-not- | override/allowlist77. A similarprogramcan be usedwith | |||||||||||||||
| calldatabase. | connectionof updating theprivateorganization list 78 and | |||||||||||||||
| Sinceitisimportant forcontrol purposes to keep track | other lists where appropriate. | |||||||||||||||
| of ss the customer companies changes in the updating | Each customer isassigned a username andthree pass- | |||||||||||||||
| database,a list ofrequestedchanges 73 ismaintained. This | words atinitial setup. Thepasswordspermit the customer | |||||||||||||||
| historicalrecord is contained in tables thatarenot | to logon to theserver andread data (logan/read password), | |||||||||||||||
| necessaryfor operation in the control computer but must | adddata totheir"Do Not Call" orMd/Override lists(add | |||||||||||||||
| be maintained to verify that the customer hasrequested | password),anddelete datafromtheir "Do NotCall"or | |||||||||||||||
| thesechanges.Whenthe customer requests an addition, a | Md/Override lists(delete password). As seen in FIG. 7, to | |||||||||||||||
| record is added to the change request table and to the | update theupdatingdo-not-call | database with | thelatest | |||||||||||||
| requested table inthisuser-interface computer. Thedateof | customercompany information, | the | customer | company | ||||||||||||
| the addrequest is part of the data entered in the change | logs on totheInternet 80 and loads | the sub.scriber web | ||||||||||||||
| request table but not in therequestedtable. After | pageSI,enters the customer nameandpassword 82. | |||||||||||||||
| verification that the requested additionhas beenmade to | 50 | |||||||||||||||
| FIG. 4 | ||||||||||||||||
| U.S. Patent |
| Sheet 4 of 6 |
| US 6,330,317 Bi |
| 65 Oncethecustomer is accepted onto the system by entering hiscorrect logon/read password, apage of options on a main menu is sent to the customer.Thiscompany-specificpage shows the companyname andother pertinent data to the customer. The data is read from the database bysearching for theusernameandreadingthe customer'scorresponding Customer Number(CN). The onlydata that the customeris |
60permittedtosee is that which is taggedby the CM that isassociated withthe company's u.sername. If thecustomerenters ausernameor passwordthat is notinthe database,or
FIG. 4
| U.S. Patent |
| Sheet 4 of 6 |
| US 6,330,317 Bi |
| US6,330,317BI |
| 9 | from thescopeandspiritoftheappended claims, they | |||||||||||
| doesnotcorrespond witheach other in the database, an | are | |||||||||||
| error | intendedto beencompassed therein. | |||||||||||
| page is sent to the customer and nodata is displayed. The | ||||||||||||
| customer cannot obtain access to unauthorized data on any | The claimsare: | |||||||||||
| page becausethe CMretrieved fromthe database at logon is | 1.A methodforblocking outgoingtelephone calls for | |||||||||||
| used to validatethecustomer's right to have the page loaded | a | |||||||||||
| in his internet browser.Thevalidation isintheformof a | numberof companies in accordance with one or more | |||||||||||
| - | ||||||||||||
| cookie that is placed on the customer's hard diskandlasts | do-not-call listscomprisingthesteps of: | |||||||||||
| onlyfor as longas thecustomer's session lasts. When the | ||||||||||||
| sessionends, the cookie disappears. The customermust | reviewing each outgoing telephone callto a telephone | |||||||||||
| enter a valid password to have thecookie placedonhis10 | switch at a | primary switch clusterof a telephone | ||||||||||
| machine. i~it isnot the correct passwordthe customer is | carrier | |||||||||||
| brought back to thesubscriberweb page 81 and asked to | todetermineif the telephone call was madefrom a | |||||||||||
| enterhisnameand password82 again. | telephonesubject to call blocking review; | |||||||||||
| Themainmenu displaysoptionsto add ordeLete | holding calls subjectto callblockingreview whilefor- | |||||||||||
| numbersfromthe customer's "Do Not Call" list or from | ||||||||||||
| thecustom-15 er'sMd/override list. Therearealso options | wardingthe | origination/destination | pairinformation | |||||||||
| correspondingtothe originating telephone numberor | ||||||||||||
| todisplayordownload any customer list. If the customer has | AuthCode andthedestinationtelephone number to | |||||||||||
| entered a | a controlcomputer; | |||||||||||
| validadd password in addition to avalid uscrnamc and | comparingthedestination numberto one or morelists | |||||||||||
| read/logon password, requeststo add anumberto one of his | ||||||||||||
| lists will be.permitted. If the customer has entered a valid20 | of | |||||||||||
| blockedtelephone numbers, said lists having | ||||||||||||
| delete password in addition to a valid usemame and rcad/ | information | relevant to more than | onecompany; | |||||||||
| logon password, requests to delete a number from one of his | and | |||||||||||
| lists will be permitted. Ifit is thecorrect password,the | dcpending only | on whether the origination/destination | ||||||||||
| customeris asked toselect a list whichitdesires to update | pair information appearson one or more of the lists, | |||||||||||
| 84. The caller is then presented with an appropriateweb ~ | eitherblockingthe telephonecall | at | the switchor | |||||||||
| page for entry ofthe dataand soenters the data 85.Entry | completingthecall. | |||||||||||
| may be byhand,by forwarding a completed~ieor by other | ||||||||||||
| means.Then thedata85is reviewed tosee ifit is in avalid | 2.Amethod | according toclaim | 1 | whereineach | ||||||||
| format86. If it is not in avalid format, the customerissent | telephone | |||||||||||
| back to reenter the data 85. If it is in avalidformat, it is | number orAuihCode correspondingto anoriginating | |||||||||||
| then 30 entered 87 intothe updating do-not-calldatabase70. | telephoneplacing acall subject to blockingreview has a | |||||||||||
| The customer is then queriedwhether therearc anymore | code associated with said number or AuthCode andthe | |||||||||||
| liststoupdate 88.If so, the customerpicks the next list to | numbersonsaidlistor | listsbeing associated with said | ||||||||||
| update 89 and enters the appropriate data85.If there arc no | code so that a telephonenumberappearingon a do-not- | |||||||||||
| furtherlists, the customer breaks the Internet connection 90. | calllist will onlyblock a call from aphone having the | |||||||||||
| The35updatingdo-not-calldatabase is periodically | associated code. | |||||||||||
| transferredtoall control computer do-not-call databases, | 3. A methodaccording tocLaim 2 whereinthelistor | |||||||||||
| usuallyonce a day at a time traffic would be at aminimum. | lists contain information | for | two or | more groupsof | ||||||||
| FIG. 8 is aflowdiagram intheprocessofupdatingthe | telephones from | which | call | originate, each group with | ||||||||
| controlcomputerdo-not-call databasebythe information | differentidentificationcodes. | |||||||||||
| contained intheupdating do-not-call database 90. First,the | 4. A methodaccordingtoclaim3whereinone of the | |||||||||||
| Internet siteforreceivingupdatinginformationfrom the | lists | |||||||||||
| customers is closed91.Thcinformation in the updating | is a listof blockednumberscompiled by anoriginating | |||||||||||
| database70 is thenbulkcopiedfortransfer92 and the | telephone group. | |||||||||||
| Internet site is reestablished to allow inputtingofdatafor the | ||||||||||||
| next updating cycle93. Thefiles are then formatted94 to | 5. Amethod accordingtoclaim 2wherein one of the | |||||||||||
| correspondtothecontrol computerdo-not-call database. | lists is a list ofblockednumbers compiled by other | |||||||||||
| Thismayincludereorganizationandintegration of files | than the | |||||||||||
| such as the statemandatedlists withtheindividuallists 94. | originatingtelephone group. | |||||||||||
| Thecontrol computer database28and29 arcreplaced with | 6.A methodaccordingto claim Swhere a destination | |||||||||||
| thedata fromthe updating database70. | appearson alistcompiledby otherthantheoriginating | |||||||||||
| It isunderstoodthatthe present embodiments described | telephone group, the number may thenbe compared with | |||||||||||
| above are to be considered asillustrativeandnotrestrictive. | anoverride list whichwould allow the call to be placed | |||||||||||
| Itwill be obvious to those skilled in the art to make various | despite appearingon saidlist compiledby otherthanthe | |||||||||||
| changes, alterations and modificationsto the invention | caller. | |||||||||||
| dcscnbed herein. For example, while particular listshavebeen | 7. A method according toclaim 6whereinthe | |||||||||||
| discussedin thebodyofthis disclosure,otherlistsmaybe | destinationnumberson the overridelistare taggedby | |||||||||||
| included or the databases may comprise entirely differentlists | originatingcaller | |||||||||||
| thanthosesetforth in the specification. The lists are~O60 be | ||||||||||||
| consideredillustrativeandnot restrictive. To the extentthat | code andthe do-not-calllistcompiled byother than a | |||||||||||
| these variations, modifications and alterations depart | group isonly overriddenwhen the overridenumberis | |||||||||||
| 10 | taggedwith | |||||||||||
FIG. 4
| U.S. Patent | Sheet 4 of 6 | US 6,330,317 Bi | ||||||||
| the number of theoriginating caller code. | switch is a switchwhichaccepts callsfromanumber of | |||||||||
| 8. Amethodaccording to claim7 wherein thedo-not- | telephones,only some of whichare | subject to | call | |||||||
| call | blocking review. | |||||||||
| listsand the overridelistsfora groupare updatedby | 10. A methodaccording to claim | 9wherein | said | |||||||
| the | telephone | |||||||||
| caller through useof theInternet. | switch is a public switch operated by a common carrier. | |||||||||
| ç;9.A method accordingto claim I wherein said telephone | ||||||||||
** *4*